HowTo: Getting an awesome Qualys SSL-Labs rating... (Feb 2017 Update)
 MVP
MVP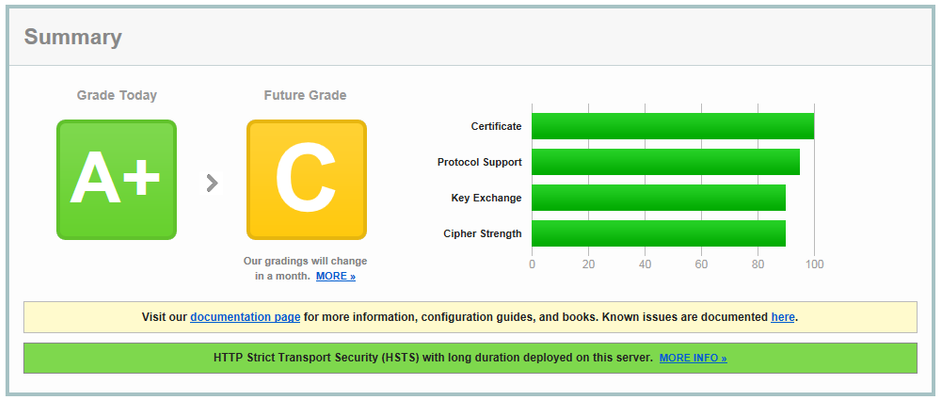
 Nimbostratus
NimbostratusKai,
Thanks...found this to be very useful in improving site security. One question though...
Per F5 (https://support.f5.com/csp/article/K13167034), in order to mitigate Sweet23 (CVE2016-2183) you need to disable all DES-CBC3 ciphers in the SSL Profile (or set the renegotiation size to 1GB). While the above Cipher list does allow for an A/A+ rating from SSL Labs, when I ran vulnerablity scans against an ssl profile with the exact cipher list above, the site was still showing vulnerable to Sweet32. I modified the Cipher list to remove any remaining DES-CBC3 ciphers and scans then came back as not-vulnerable to Sweet32.
Here's my Cipher-list after I took into account the F5 recommendation to remove all DES-CBC3:
!SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:!DHE+3DES:!ECDHE-RSA-DES-CBC3-SHA:!ECDHE-ECDSA-DES-CBC3-SHA:!ADH-DES-CBC3-SHA:!ECDH-RSA-DES-CBC3-SHA:!ECDH-ECDSA-DES-CBC3-SHA:!DES-CBC3-SHA:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:ECDHE+3DES:RSA+3DES:-MD5:-SSLv3:-RC4For readability, here's the diff in what I added to the Cipher List:
!ECDHE-RSA-DES-CBC3-SHA:!ECDHE-ECDSA-DES-CBC3-SHA:!DHE-RSA-DES-CBC3-SHA:!ADH-DES-CBC3-SHA:!ECDH-RSA-DES-CBC3-SHA:!ECDH-ECDSA-DES-CBC3-SHA:!DES-CBC3-SHAYour thoughts?