HowTo: Getting an awesome Qualys SSL-Labs rating... (Feb 2017 Update)
 MVP
MVP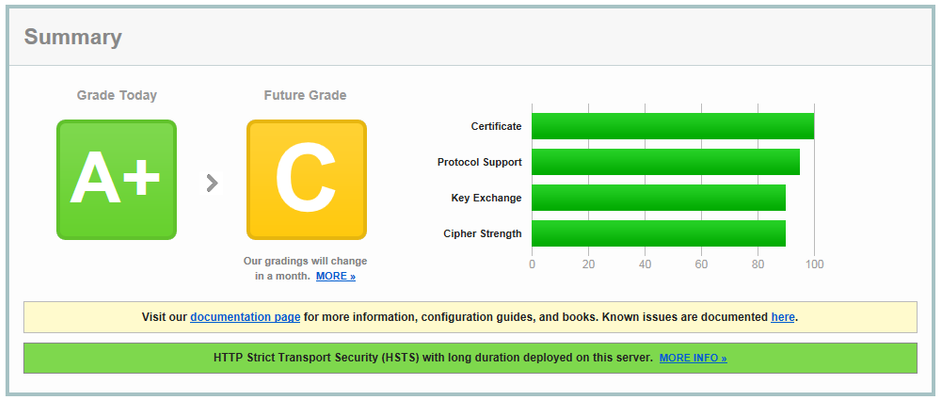
 Nimbostratus
NimbostratusHey Kai. This is fantastic stuff. I don't know anything about making even the slightest tweak to these. Could you assist with the string I would need for TLS 1.1 and 1.2 ciphers only, with no 3DES and RSA key exchanges at the bottom of my list?
 Nimbostratus
NimbostratusThis is AMAZING, thank you!!
 MVP
MVPYou're pretty much welcome. Let me know if you need some extra clarification or assistance... ;-)
Cheers, Kai
 Nimbostratus
NimbostratusHi Kai,
As of today, what would be the best Ciphers suite which will give A+ from SSL-Labs? can i consider below one? I have taken all three from this thread only.
i am using v13.0.0 with HF3
!SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:-MD5:-SSLv3:-RC4:!3DES
!SSLv2:!EXPORT:!DHE:!3DES:RSA+AES-GCM:RSA+AES:ECDHE+AES-GCM:ECDHE+AES:!MD5:!SSLv3:!RC4
!SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:!DHE+3DES:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:ECDHE+3DES:RSA+3DES:-MD5:-SSLv3:-RC4
 MVP
MVPHi Harry,
depends what exactly means "best" for you? Choosing the right cipher suite is basically a pendulum between "Security" and "Compatibility"...
The most balanced cipher string is in my opinion this one...
ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-CBC-SHA:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES128-CBC-SHA:AES256-GCM-SHA384:AES128-GCM-SHA256:AES256-SHA256:AES256-SHA:AES128-SHA256:AES128-SHA:DES-CBC3-SHA:-SSLv3:-DTLSv1
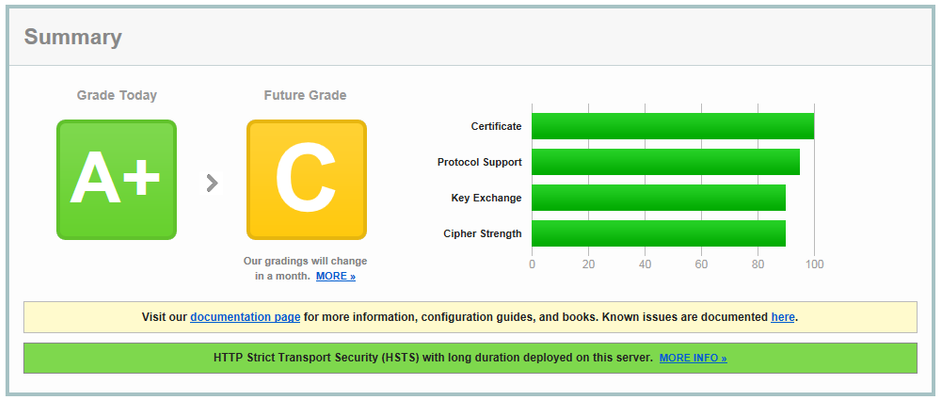
The chipher string has support for all modern ciphers (in a prefered order) but its compatible down to WinXP/IE8 and achives a A+ rating in combination with HSTS settings.
Note: The cipher string above still uses DES algorythms for legacy browser. Because of this you have to tweak your Client_SSL_Profile so that you renegotiate the SSL session every 1024Mbyte transfered data to counter Sweet32 attacks.
If you don't care about old browsers, then this one is also a good balance...
ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-CBC-SHA:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES128-CBC-SHA:AES256-GCM-SHA384:AES128-GCM-SHA256:AES256-SHA256:AES256-SHA:AES128-SHA256:AES128-SHA:-SSLv3:-TLSv1:-DTLSv1
Cheers, Kai
 Nimbostratus
NimbostratusThanks Kai. i got A Grade with first one.
 Nimbostratus
NimbostratusI posted to the older thread, here's my update. First, thanks to Kai for starting this thread and providing the info, excellent!
With the recent publication of ROBOT attach on the RSA cipher, I have added !RSA to my cipher profile and tested with no issues. https://support.f5.com/csp/article/K21905460proc1
What is the stand on TLS 1.3
 Nimbostratus
NimbostratusI'm running 11.6.3 and enabling "single DH use" does not remove the warning about "ECDH public server param reuse"
edit: I take that back, it does work but it seemed to take a while or wasn't picked up by SSLlab's additional scans.
 Nimbostratus
NimbostratusHi Kai,
I was looking for 'fix' for this particular issue and i found this thread that you posted. :)
https://support.f5.com/csp/article/K13400config_p1
as we were recently been flagged out by the recent pen test. Our client basically just want to disable the TLSv1 as per F5 recommendation.
SSL is not really my strong suit. :) And based from what i have read, i understand that i just need to change the clientssl profile configuration and enable TLSv1_2 but im not really sure whether that is all the cipher that i need to enable or all that i need to do to achieve that? How about the ciphersuite for restricting the configuration utility to use only TLSv1.2?
Basically, i just need to know what would be the best cipher suit for this? :) we are currently running 12.1.2 HF1.
Btw, we currently only have 2 VS that is using the SSL profile and it is using the default clientssl and server profile.
Here is our current Cipher suite: ECDHE-RSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-RSA-AES256-SHA:ECDHE-RSA-AES128-SHA256:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA:ECDHE-ECDSA-AES128-SHA256:ECDHE-ECDSA-AES256-SHA384:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA:AES256-SHA:AES128-SHA256:AES256-SHA256:ECDHE-RSA-DES-CBC3-SHA:ECDHE-ECDSA-DES-CBC3-SHA:DES-CBC3-SHA
 Nimbostratus
NimbostratusHello, I read this article and add one option on the end - reduce week Cipher Suites. I hope that this combination it's ok - Please check new combination. Br. Darek
ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-CBC-SHA:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES128-CBC-SHA:AES256-GCM-SHA384:AES128-GCM-SHA256:AES256-SHA256:AES256-SHA:AES128-SHA256:AES128-SHA:-SSLv3:-TLSv1:-DTLSv1:!RSA
 Cirrostratus
CirrostratusKia, I've been following this and your previous thread, it has been very helpful!!
I have what may be an old cipher suite set with: !SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:!DHE+3DES:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:ECDHE+3DES:RSA+3DES:-MD5:-SSLv3:-RC4
Before I try a new Cipher suite all together, is there a conflict in using the above Cipher suite and specifically disabling TLSv1, whether in the GUI options or adding !TLSv1 to the list of ciphers?
Can I add No TLSv1 in the options list while using the above Cipher Suite?
Is this a bad, or invalid Cipher Suite? !TLSv1:!SSLv2:!EXPORT:!DHE+AES-GCM:!DHE+AES:!DHE+3DES:ECDHE+AES-GCM:ECDHE+AES:RSA+AES-GCM:RSA+AES:ECDHE+3DES:RSA+3DES:-MD5:-SSLv3:-RC4