Stable Firmware for F5
Hi All, Currently we have f5 BIG-IP i5600 appliance in our environment. The current firmware version is 15.1.10, we are planning to upgrade the firmware to the n-1 patch or next stable version. I'm new to F5. Can anyone suggest an stable version or guide how to check for the feasible firmware version. The main feature that we use in F5 is Load balancer and we enabled ASM policies for the VIPs. So there should not be any impact on the existing function. Thanks in Advance. Karmegha Kuzhali.15Views0likes1CommentF5 VE in Azure - troubles with Sentinel integration
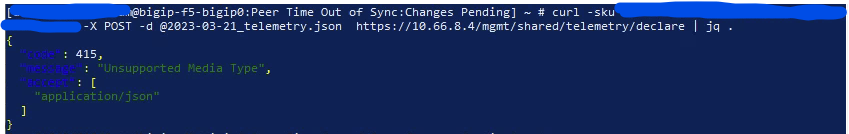
Hi! I'm having F5 Act/Stb cluster - 2 VMs in Azure with 2 traffic interfaces only (external, internal). I use BIG-IP 16.1.3 build 0.0.12 I'm trying for the first time in my life integrate it with Sentinel and so far I fail to do it succesfully. When following this article:https://my.f5.com/manage/s/article/K85539421point by point: Install telemetry extension goes well. I have 1.32.0 build 2 version (downloaded today). curl check is succesful Create iRule - done Create a pool to handle telemetry traffic - ends up with down by monitor. (Manual suggests to use tcp monitor). I tried to support with hints from: https://community.f5.com/t5/technical-articles/deploying-big-ip-telemetry-streaming-with-azure-sentinel-as-its/ta-p/278738, where people suggest to add static route the via internal vlan: net route telemetry { description "Allows monitor to work" interface /Common/internal network 255.255.255.254/32 or changing port lockdown mode: "One more note: the self IP on the chose VLAN you're using for routing the 255.255.255.254 traffic needs to allow TCP 6514, either by setting the "port lockdown" to NONE or adding a custom port." I tried to finish the manual, so: Create a virtual server to listen for Telemetry traffic Create a request-log profile Attach the request logging profile to the virtual server And when it comes to deploy the declaration (which I do via curl with .json file, I get: Has anyone passed through some manual integrating F5 with Azure Sentinel succesfully? Or maybe I'm doing here some obvious mistake? Thanks in advance for your help987Views0likes2CommentsNeed help on i-rule to specific uri path
Hello All, I'm working on an i-rule that I need to do the following; given a set of specific source ip addresses, only allow access to specific uris of /ws/rest/external*. I set the specific source addresses in a data group, referencing the data group. When I apply this i-rule to the virtual server, on testing I get an Insecure HTTPS message. I am on version 15.8.1.2. We plan to upgrade to most stable release on 16 soon. Any suggestions on what I can do with the i-rule posted below? Thanks in advance. when CLIENT_ACCEPTED { if { [class match [IP::client_addr] equals Boomi_external] } { pool esd-bmapi-dc1-as01-f5.lanl.gov_8077_pool } } when HTTP_REQUEST { if ![HTTP::has_responded] { if { ([HTTP::host] equals "apigway-d.lanl.gov" or [HTTP::host] equals "apigway-d.lanl.gov") } { if { [HTTP::uri] starts_with "/ws/rest/external* " || [HTTP::uri] starts_with "/ws/rest/external*" } { pool esd-bmapi-dc1-as01-f5.lanl.gov_8077_pool } else { reject } return } } }7Views0likes0CommentsLDAPS and renegotiation
Hello, hope everyone is well! we have a requirement to present 2 different issuer/signed certificates based on the incoming client IP. I am pretty sure from an HTTP perspective I would do something like this when CLIENT_ACCEPTED { if {([class match [IP::client_addr] eq signer_list_of_client_A_IPs]) } { SSL::profile cert_with_issuer_type_A } else { SSL::profile cert_with_issuer_type_B } } when HTTP_REQUEST { SSL::renegotiate } Question I have is whether this would work for LDAPS clients and how (if needed at all) the renegotiation step would be achieved, given that the HTTP_REQUEST will not be available. Many thanks Jon6Views0likes0CommentsF5 Rseries HA
Dears, I know that there is no HA between rseries appliance, and the HA will be configured between tenants on each appliance, my question her about when i prepare to configure HA between Tenant so before making this i will configure the network setting and VLAN on F5OS so I will need a dedicated interface and HA VLAN between two tenants on each appliance so what is the next step after I configured the network setting on Appliance (F5OS), and what i need to confirm on the network setting that i will configure on each appliance (F5OS) to make HA between the two tenants29Views0likes2CommentsCan iRule be used to perform exception of IPI category based on Geolocation
Hi Everyone, Can we configure iRule to perform exception on certain IPI category like "Spam Sources" based on Geolocation. For instance, I want to bypass the mitigation enforced on "Spam Sources" IP intelligence category for "Nepal" -Geolocation specific because of the large false positives on this category. I found the iRules to enforce the mitigation based on the defined IPI category: when HTTP_REQUEST { set ip_reputation_categories [IP::reputation [IP::client_addr]] set is_reject 0 if {($ip_reputation_categories contains "Windows Exploits")} { set is_reject 1 } if {($ip_reputation_categories contains "Web Attacks")} { set is_reject 1 } if {($is_reject)} { log local0. "Attempted access from malicious IP address [IP::client_addr] ($ip_reputation_categories), request was rejected" HTTP::respond 200 content "<HTML><HEAD><TITLE>Rejected Request</TITLE> </HEAD><BODY>The request was rejected. <BR> Attempted access from malicious IP address</BODY></HTML>" } } https://techdocs.f5.com/en-us/bigip-15-0-0/big-ip-local-traffic-manager-implementations/enabling-ip-address-intelligence.html3Views0likes0CommentsCan iRule mask the payload content on event logs of security
Hello Everyone, Is it possible to mask the certain value of the request on the Application Security > Event Logs using iRule, Since the application "Content-Type: application/octet-stream" and the payload consists some sensitive information of the user which are not associated with any parameters in the payload. The requested URL is "/api/v1/client/client-auth/login" and I want to mask the content after first value (which is a cell number and follows a pattern) till the 15 characters, regardless of the character used. The payload sample: 9844445555 password@123 I tried with a below iRule script but the application stopped working: when HTTP_REQUEST { if { [HTTP::uri] equals "/api/v1/client/client-auth/login" && [HTTP::header "Content-Type"] equals "application/octet-stream" } { set payload [TCP::payload] set pattern {(\d+).*?} if {[regexp -indices $pattern $payload match_indices]} { foreach {start_index end_index} $match_indices { set dynamic_length [expr {$end_index - $start_index - 10}] ; set masked_part [string repeat "*" $dynamic_length] set masked_payload [string replace $payload [expr $start_index] [expr $end_index - 1] $masked_part] set payload $masked_payload } TCP::payload replace 0 [string length $payload] $payload } } }72Views0likes4CommentsPricing when used with aws waf
Hi, Want to understand how pricing is calculated for F5 WAF rules. when we say price is Charge per month in each available region (pro-rated by the hour)$20 / unit Charge per million requests in each available region$1.2 / unit What unit represent here ? When used with AWS WAF, would it be in addition to what aws is already charging based on their capacity units ? Thanks10Views0likes1CommentAdvise on setting up IRULE
getting error " HTTP_ Request event in rule requires an associated HTTP or FASTHTTP profile on virtual server My requirement When client request for URL https://netforum.rotaryintl.org/xwebevents it should hit the pool NF_PRD_XWEBEVENTS_443 AND When the client request for URL https://netforum.rotaryintl.org it should hit the pool Netforumprd_443_Pool Current SETUP VIP is configured with port set to 44345Views0likes5Comments