F5 Partners join us for Partner Connect Quarterly Update: May 21 & 22
We are excited to invite you to the F5 Partner Connect Quarterly Update, an exclusive event designed to empower our partners with cutting-edge insights and strategic direction. Join us on May 21st and 22nd for a deep dive into F5's transformation journey and the unlocking of API security potential. May 21 12pm SGT: Asia Pacific, China, and Japan May 22: 2pm BST: Europe, Middle East, and Africa 11am PDT: Americas We will revisit F5’s evolution and reinforce our stance on API security, spotlighting our strategic acquisitions of WIB and Heyhack. Chuck Herrin, Senior Principal Product Manager for Security and former CTO at WIB, will delineate F5's forward-thinking approach in the application and API security landscape. Josh Goldfarb, Global Solutions Architect for Security will present 10 actionable best practices. These insights will help you, our valued partners, to maximize profitability and leverage F5’s innovative solutions for unparalleled market opportunities. Do not miss this chance to connect with F5 leaders and stay at the forefront of the security domain. Together, let's transform challenges into opportunities and elevate API security to new heights. Register Now!21Views0likes0CommentsHow I did it - "Remote Logging with the F5 XC Global Log Receiver and Elastic"
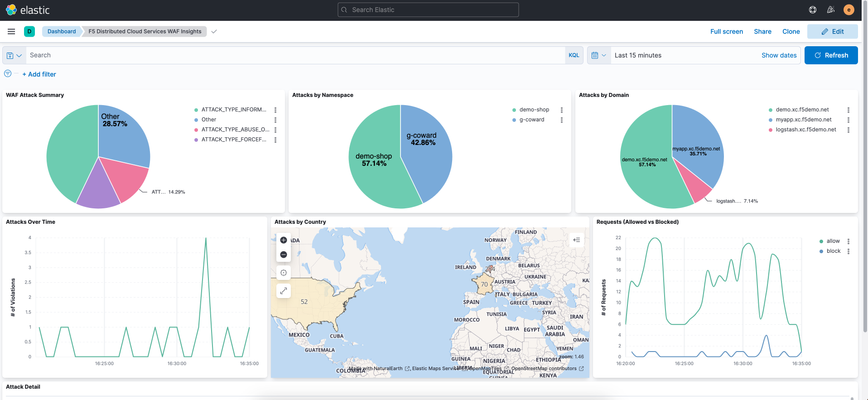
Welcome to configuring remote logging to Elastic, where we take a look at the F5 Distributed Cloud’s global log receiver service and we can easily send event log data from the F5 distributed cloud services platform to Elastic stack.193Views1like0Comments- 236Views0likes0Comments
A Makeover for DevCentral.
UPDATE: This maintenance has been moved to Jan 24th starting at approximately 8AM Pacific time. --- DevCentral Community, TL;DR - I am announcing some updates coming to the DevCentral community website in a few days - January 17th.24th. This is a mid-sized reboot, some upgrades that we expect will make our online environment a bit nicer to use now and enable more epic-ness to come. ***This update WILL include a maintenance downtime of up to 6 hours starting around 8AM PT (-8 UTC).*** A huge shoutout. I speak for everyone on our team when I say the DevCentral community rocks! We on the DevCentral team are inspired and motivated by your creativity and willingness to share. The depth of your capabilities and the mutual respect you have for individual learning never ceases to amaze. Asyou, collectively, work through increasingly complex problem-spaces we are always working to support your progress. Our recent observations and your suggestions have been buzzing in our ears for several months and so the changes you'll see soon represent next steps for what we think will make your DevCentral community truly exceptional. An updated UI is just the start. Interface updates will be the most obvious, but these are evolutionary rather than revolutionary - a paint job and some new tech. The new tech includes a simpler set of stylesheets, more configurable page templates, some advanced features in the editors, and an overall reductive approach to some historical bloat. One of my design tenets is best summarized as comfortably information dense. DevCentral is a functional website, mostly used during your workweek, and we are looking to strike a balance between engaging with the content quickly and easily (e.g., less scrolling and more filters) without getting eyestrain or needing to know where you are on the site. I'll get into a bit more detail next week and after we launch, I expect to produce some guided walkthroughs you can use to discover some gems. If you are coming to AppWorld in San Jose in February - be sure to stop by our booth and look me up - I can give you a personalized tour.Mention this article and I'll be forced to find some special swag for you too!😎 Wait. Did you say "reductive"? Yes. In a world where everyone backs up everything a subtractive mindset seems nutty. I'm no expert (case-in-point, the length of this announcement) but I embrace the subtractive sentiment and as such I have been ruthless about driving this upgrade for a host of reasons and that *may* have come at the expense of some existing features. Some things won't be present at launch (like Badges and Event calendars) but on-balance I'm sure we will be better off. That said, if something you love disappears - let me know in a comment, in a DM, or on the Suggestions page. I can't promise everything, butI do promise my level-best and that everything is done with intent: sharing valuable and useful technical information with you. Temporary Outage Most important, for now, is to plan for a short outage the morning of Jan 17th approximately 8AM Pacific Time (-8H UTC) for up to about 6 hours. Next: A reminder on Monday, Jan 15th 🚀509Views8likes7CommentsReasons to attend AppWorld
From February 6-8 at McEnery Convention Center in San Jose, California, AppWorld 2024 attendees will have access to technical breakouts, labs, executive keynote speakers, a panel of AppSec Experts, the DevCentral team and community members, F5 partners, and more! The panel of AppSec experts includes former CISO of Twitter and OWASP Chairman of the Board Michael Coates who is currently the CISO and VP of Engineering at CoinList; Howard Patty, Senior Manager of Technology for Digital Platforms at Southwest Airlines; Lee Waskevich, ePlus VP of Security and Networking Strategy; and F5 Distinguished Engineer Lori Mac Vittie. For more information and to register, clickhere.130Views2likes0CommentsSecurity Automation with F5 BIG-IP and Event Driven Ansible
Updated (September 19th 2023) INTRODUCTION TO EVENT DRIVEN SECURITY: Event Driven Security is one of the projects I have been working on for the last year or so. The idea of creating automated security that can react similarly to how I would react in situations is fascinating to me, and then comes the BIG Question.... "Can I code it?" Originally our solution we had utilized ELK (Elastic Logstash Kibana) where Elasticsearch was my logging and monitoring tool, Kibana was the frontend GUI for helping me visualize and set up my watchers for my webhook triggers, Logstash would be an intermediary to receive my webhooks to help me execute Ansible related code. While using Logstash, if the Ansible code was simple it had no issues, however when things got more complex (i.e., taking payloads from Elastic and feeding them through Logstash to my playbooks), I would sometimes get intermittent results. Some of this could be my lack of knowledge of the software but for me it needed to be simple! As I want to become more complex with my Event Driven Security, I needed a product that would follow those needs. And luckily in October 2022 that product was announced "Event Driven Ansible" it made it so I didn’t need Logstash anymore i could call Ansible related code directly, it even took in webhooks (JSON based) to trigger the code, so I was already half way there! CODE FOR EVENT DRIVEN SECURITY: So now I have setup the preface let’s get down to the good stuff! I have setup a GitHub repository for the code i have been testing withhttps://github.com/f5devcentral/f5-bd-ansible-eda-demowhich is free for all to use and please feel free to take/fork/expand!!! There are some cool things worth noting in the code specifically the transformation of the watch code into something usable in playbooks. This code will take all the times the watcher finds a match in its filter and then then copies the Source IP from that code and puts it into a CSV list, then it sends the list as a variable within the webhook along with the message to execute the code. Here is the code I am mentioning above about transforming and sending the payloads in an elastic watcher. See the Full code in the GitHub repo. (Github Repo --> elastic -->watch_blocked_ips.json) "actions": { "logstash_exec": { "transform": { "script": { "source": """ def hits = ctx.payload.hits.hits; def transform = ''; for (hit in hits) { transform += hit._source.src_ip; transform += ', ' } return transform; """, "lang": "painless" } }, "webhook": { "scheme": "http", "host": "10.1.1.12", "port": 5000, "method": "post", "path": "/endpoint", "params": {}, "headers": {}, "body": """{ "message": "Ansible Please Block Some IPs", "payload": "{{ctx.payload._value}}" }""" } } } } In the Ansible Rulebook the big thing to note is that from the Pre-GA code (which was all CLI ansible-rulebook based) to the GA version (EDA GUI) rulebooks now are setup to call Ansible Automation Platform (AAP) templates. In the code below you can see that its looking for an existing template "Block IPs" in the organization "Default" to be able to run correctly. (Github Repo --> rulebooks -->webhook-block-ips.yaml) --- - name: Listen for events on a webhook hosts: all ## Define our source for events sources: - ansible.eda.webhook: host: 0.0.0.0 port: 5000 ## Define the conditions we are looking for rules: - name: Block IPs condition: event.payload.message == "Ansible Please Block Some IPs" action: run_job_template: name: "Block IPs" organization: "Default" This shows my template setup in Ansible Automation Platform 2.4.x, there is one CRITICAL piece of information i wanted to share about using EDA GA and AAP 2.4 code is that within the template you MUSTtick the checkbox on the "Prompt on launch" in the "variables section". This will allow the payload from EDA (given to it from Elastic) to pass on to the playbook. In the Playbook you can see how we extract the payload from the event using the ansible_eda variable, this allows us to pull in the event we were sent from Elastic to Event Driven Ansible and then sent to the Ansible Automation Platform template to narrow down the specific fields we needed (Message and Payload) from there we create an array from that payload so we can pass it along to our F5 code to start adding Blocked IPs to the WAF Policy.(Github Repo --> playbooks -->block-ips.yaml) --- - name: ASM Policy Update with Blocked IPs hosts: lb connection: local gather_facts: false vars: Blocked_IPs_Events: "{{ ansible_eda.event.payload }}" F5_VIP_Name: VS_WEB F5_VIP_Port: "80" F5_Admin_Port: "443" ASM_Policy_Name: "WAF-POLICY" ASM_Policy_Directory: "/tmp/f5/" ASM_Policy_File: "WAF-POLICY.xml" tasks: - name: Setup provider ansible.builtin.set_fact: provider: server: "{{ ansible_host }}" user: "{{ ansible_user }}" password: "{{ ansible_password }}" server_port: "{{ F5_Admin_Port }}" validate_certs: "no" - name: Blocked IP Events From EDA debug: msg: "{{ Blocked_IPs_Events.payload }}" - name: Create Array from BlockedIPs ansible.builtin.set_fact: Blocked_IPs: "{{ Blocked_IPs_Events.payload.split(', ') }}" when: Blocked_IPs_Events is defined - name: Remove Last Object from Array which is empty array object ansible.builtin.set_fact: Blocked_IPs: "{{ Blocked_IPs[:-1] }}" when: Blocked_IPs_Events is defined ... All of this combined, creates a well-oiled setup that looks like the following diagram below, with the code and the flows setup we can now create proactive event based security! Here is the flow of the code that is in the GitHub repo when executed. The F5 BIG-IP is pushing all the monitoring logs to Elastic. Elastic is taking all that data and storing it while utilizing a watcher with its filters and criteria, The Watcher finds something that matches its criteria and sends the webhook with payload to Event Driven Ansible. Event Driven Ansible's Rulebook triggers and calls a template within Ansible Automation Platform and sends along the payload given to it from Elastic. Ansible Automation Platforms Template executes a playbook to secure the F5 BIG-IP using the payload given to it from EDA (originally from Elastic). In the End we go Full Circle, starting from the F5 BIG-IP and ending at the F5 BIG-IP! Full Demonstration Video: Check out our full demonstration video we recently posted (Sept 13th 2023) is available on-demand viahttps://www.f5.com/company/events/webinars/f5-and-red-hat-3-part-demo-series This page does require a registration and you can check out our 3 part series. The one related to this lab is the "Event-Driven Automation and Security with F5 and Red Hat Ansible" Proactive Securiy with F5 & Event Driven Ansible Video Demo LINKS TO CODE: https://github.com/f5devcentral/f5-bd-ansible-eda-demo1.8KViews10likes0Comments