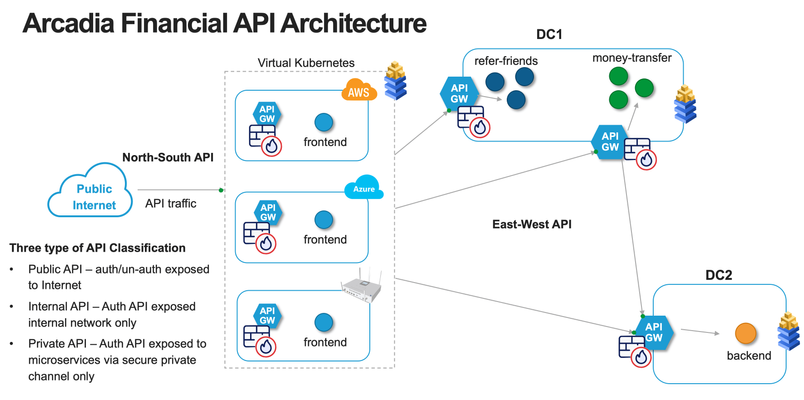
API Security Strategy - Discover and map APIs, block unwanted connection and prevent data leakage
Updated Jan 04, 2023
Version 3.0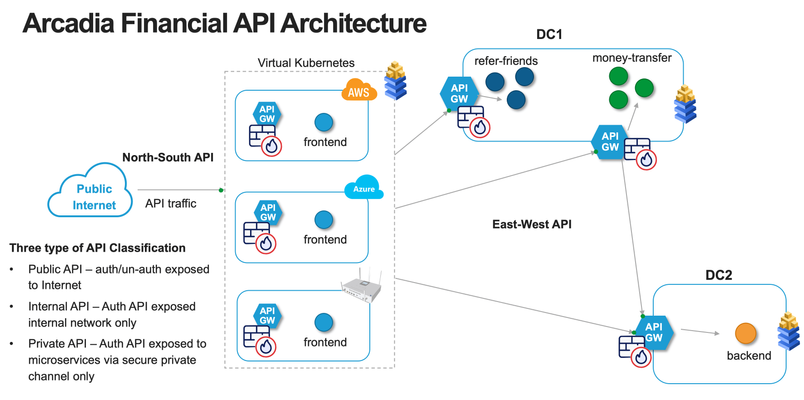
Was this article helpful?
 Employee
EmployeeFantastic article, Foo Bang!
APIs are like snowflakes. Each one must be protected in the right way. I especially like the way the shadow API is called out in the example above.